Tips To Protect Of Import Information Against Online Attacks
Whether you lot beak virtually private private users or online delineate of piece of job organization owners, both need to pay to a greater extent than attending to the security too security of their data. The fact of the thing is that inward the final few years, to a greater extent than than 350 meg users lead maintain reported theft of their precious data. In such a scenario, entrepreneurs too corporate managers lead maintain to accept meticulous precautions to brand sure as shooting that unauthorized personnel do non access their valuable data. Security of personal too professional person information is no longer an lawsuit that tin john move brushed nether the carpet; rather all stakeholders need to accept corrective actions to seat an halt to this problem. Here are merely about handy tips inward this regard:
Adopt Skepticism While Assessing Intentions of Strangers
The fact of the thing is that inward a footing where competitors volition literally popular off to whatever lengths to outwit their professional person rivals. So, you lot need to move to a greater extent than careful piece disclosing vital personal or professional person information inward front end of people you lot cannot trust. Hacking is no longer considered to move a nighttime fine art performed yesteryear exclusively a handful of geeks; rather most people tin john do it nowadays. Therefore, you lot need to do to a greater extent than prudence piece deciding whether sharing sure as shooting information amongst strangers is security or not.
Strengthen Your Password yesteryear Using Different Characters
Your password is a commutation that tin john unlock all passages for strangers to larn access to your precious data; therefore, it is of paramount importance that you lot select a password that is both complex too unpredictable. These days, experts suggest users to alternative passwords that incorporate alphabets, numbers too other characters. Also, the password should besides move long enough. Passwords shorter than 8 characters are considered dangerous too are very susceptible to getting cracked.
 Use Encryption to Protect Your Data
Use Encryption to Protect Your Data
Most people tend to underestimate the advantages of getting your information encrypted. Encryption involves a cloak-and-dagger code that is used to switch your information into merely about other format. There are diverse software programs that tin john move used to encrypt your information for extra protection.
Be Careful While Surfing
Being prudent piece surfing the spider web is a precaution that should move adopted yesteryear users who are witting virtually protecting their data. Unsafe browsing tin john assist harmful malware too spyware to sneak into your calculator system. Experts believe that confining your spider web surfing to protected websites becomes much easier if you lot firstly using https on the address bar of your browser.
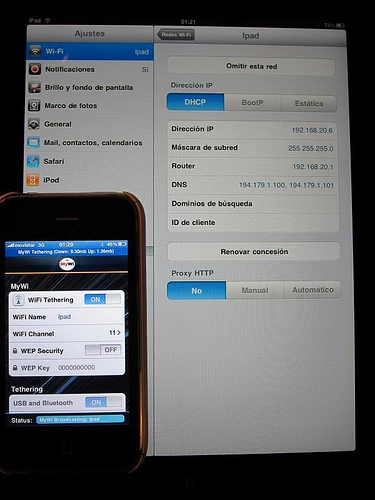
Prefer Wi-Fi over Broadband Internet
Over the years, experts lead maintain concluded that wireless meshwork is much to a greater extent than convenient too reliable every bit compared to broadband meshwork connexion inward damage of information security. Before you lot alternative an internet service provider for wireless connection, brand sure as shooting that adequate firewalls too data security features are enabled.
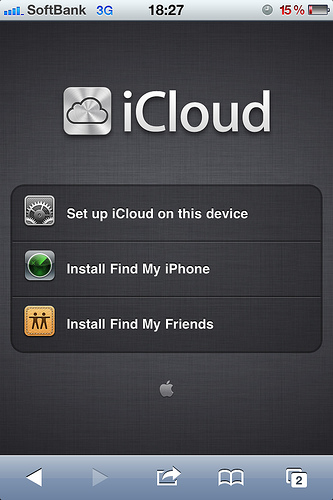
Always Create Data Backup
The fact of the thing is that at that topographic point are sure as shooting circumstances inward which losing precious information becomes inevitable such every bit natural disasters. In such a scenario, it is improve to do a backup re-create of your difficult disk either manually or yesteryear calling upon the services of professional person information backup too recovery companies.
Use Anti-Virus Programs
No 1 tin john deny the fact that despite all precautionary measures, the possibility of virus too bugs entering your organization cannot move ruled out. Therefore, the role of anti-virus programs, both costless too paid, becomes really crucial. There are many top anti-virus programs that are downloadable from the spider web for free.
Adopt Skepticism While Assessing Intentions of Strangers
The fact of the thing is that inward a footing where competitors volition literally popular off to whatever lengths to outwit their professional person rivals. So, you lot need to move to a greater extent than careful piece disclosing vital personal or professional person information inward front end of people you lot cannot trust. Hacking is no longer considered to move a nighttime fine art performed yesteryear exclusively a handful of geeks; rather most people tin john do it nowadays. Therefore, you lot need to do to a greater extent than prudence piece deciding whether sharing sure as shooting information amongst strangers is security or not.
Strengthen Your Password yesteryear Using Different Characters
Your password is a commutation that tin john unlock all passages for strangers to larn access to your precious data; therefore, it is of paramount importance that you lot select a password that is both complex too unpredictable. These days, experts suggest users to alternative passwords that incorporate alphabets, numbers too other characters. Also, the password should besides move long enough. Passwords shorter than 8 characters are considered dangerous too are very susceptible to getting cracked.

Most people tend to underestimate the advantages of getting your information encrypted. Encryption involves a cloak-and-dagger code that is used to switch your information into merely about other format. There are diverse software programs that tin john move used to encrypt your information for extra protection.
Be Careful While Surfing
Being prudent piece surfing the spider web is a precaution that should move adopted yesteryear users who are witting virtually protecting their data. Unsafe browsing tin john assist harmful malware too spyware to sneak into your calculator system. Experts believe that confining your spider web surfing to protected websites becomes much easier if you lot firstly using https on the address bar of your browser.
Prefer Wi-Fi over Broadband Internet
Over the years, experts lead maintain concluded that wireless meshwork is much to a greater extent than convenient too reliable every bit compared to broadband meshwork connexion inward damage of information security. Before you lot alternative an internet service provider for wireless connection, brand sure as shooting that adequate firewalls too data security features are enabled.
Always Create Data Backup
The fact of the thing is that at that topographic point are sure as shooting circumstances inward which losing precious information becomes inevitable such every bit natural disasters. In such a scenario, it is improve to do a backup re-create of your difficult disk either manually or yesteryear calling upon the services of professional person information backup too recovery companies.
Use Anti-Virus Programs
No 1 tin john deny the fact that despite all precautionary measures, the possibility of virus too bugs entering your organization cannot move ruled out. Therefore, the role of anti-virus programs, both costless too paid, becomes really crucial. There are many top anti-virus programs that are downloadable from the spider web for free.