Make Facebook Photos & Posts Private
Do you lot stimulate got private pictures of yourself or your household unit of measurement on Facebook which you lot don't desire the entire globe to see? This direct volition aid you lot alter your Facebook privacy settings to exclusively permit your friends or people you lot know to run across your Facebook photos (and everything else you lot do). You tin fifty-fifty customize the privacy settings of private albums to portion them alongside a small-scale grouping of people similar your co-workers or relatives.
 There are iii ways inwards which you lot tin exercise this. Either, you lot tin customize each wall post's or photo's settings individually, or develop the preferences for specific albums or utilisation a full general setting for all posts together with photos you lot have.
There are iii ways inwards which you lot tin exercise this. Either, you lot tin customize each wall post's or photo's settings individually, or develop the preferences for specific albums or utilisation a full general setting for all posts together with photos you lot have.
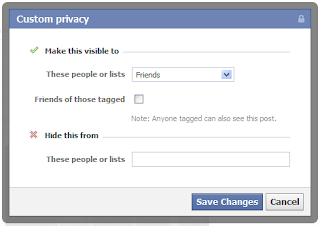
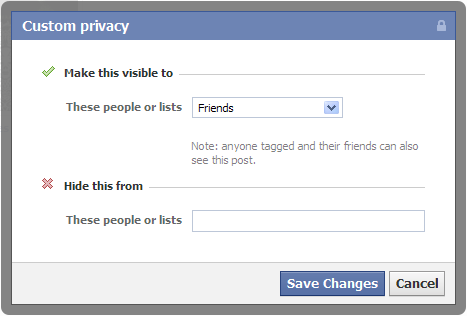
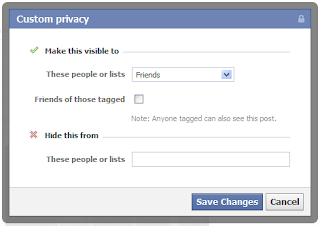
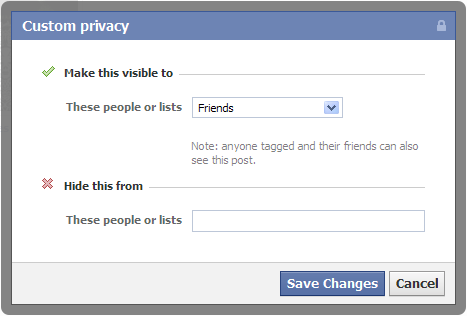
You tin fifty-fifty enshroud a photograph from specific people or a listing of people. This volition hold upwards particularly useful inwards situations where you lot don't desire your colleagues to run across a sure enough motion-picture exhibit that makes fun of them or something similar. Normally, when someone is tagged inwards a photo, every friend of that Facebook user gets to know well-nigh it. So, if you lot chose to brand a photograph visible to friends together with someone is tagged inwards that picture, all their friends volition run across that image. To preclude this, uncheck the Friends of those tagged checkmark.
All those people who are tagged together with their friends would soundless hold upwards able to run across the photos inwards your album. To preclude this, you lot volition stimulate got to alter the privacy settings of each private photo.
Step 1: Limiting Past Posts & Photos
Go to your Privacy Settings, together with therefore become to "Limit the audience for posts you've shared alongside friends of friends or Public?." Then click on the "Limit Old Posts" button. In the pop-up, click Confirm. This is a permanent alter together with cannot hold upwards undone. However, all those tagged together with their friends would soundless hold upwards able to run across your posts. To preclude this, you lot volition stimulate got to alter each post's settings individually.
Step 2: Limiting Future Posts together with Photos
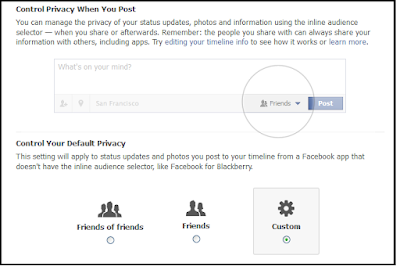
While inwards the privacy center, click on "Who tin run across your hereafter posts?" This volition opened upwards a non-functional condition update box. However, the privacy options that opened upwards when clicking on the downward arrow correct side past times side to the postal service push clit are functional together with deed equally global defaults for the content you lot postal service on Facebook inwards the future. Make sure enough to choose friends if you lot exclusively wishing to portion content alongside your friends. You tin however, alter this according to your needs; but for most people, friends would hold upwards the best option. You tin farther meliorate your privacy past times selecting Custom together with therefore unchecking the banking concern friction match box that appears side past times side to "Friends of those tagged". This volition customize your Facebook settings to exhibit your Facebook activeness exclusively to your friends together with those tagged.
You tin too choose who gets tagged inwards your content to farther preclude your content from appearing inwards forepart of unwanted eyes. To exercise this, become to your Privacy Settings from the Settings icon located at the locomote on correct of the bluish Facebook bar. Then, inwards Privacy Settings, click on Timeline together with Tagging. Then under, "How tin I create exercise tags people add together together with tagging suggestions?", choose Enabled to review tags that friends add together to your posts.
Facebook's privacy settings accept roughly fourth dimension to suit but in i lawsuit you lot are done, you lot volition never stimulate got to worry well-nigh your content ending upwards inwards forepart of unwanted users.
Related: Stop Hackers on Facebook

1: Choosing an private wall post's or photo's privacy settings
While posting your photograph or post, click on the downward arrow left to the postal service button. Select Custom from the drop-down menu. Using the pop-up, choose who you lot wishing to brand a postal service visible to. You tin choose if you lot wishing to exhibit a postal service to friends, friends of friends or specific people or a specific listing of people. |
| Select Custom Privacy Options |
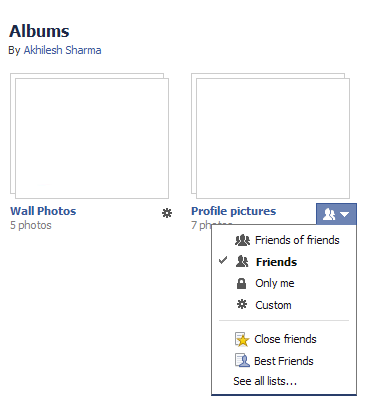
2: Limiting the Audience for an entire album
This is much similar to setting the audience for an private picture. Just become to your albums, click on the Settings icon on the bottom correct of the album whose privacy settings you lot wishing to customize. Then choose Custom from the drib downward menu. The options Facebook offers are almost the same equally those for an private photo, notwithstanding at that topographic point is i difference.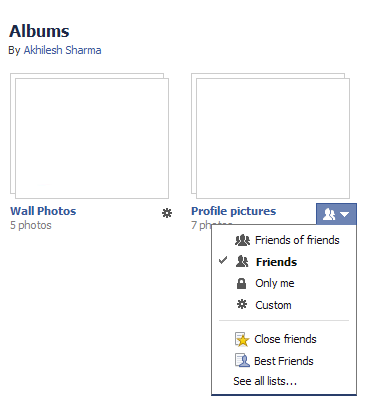
All those people who are tagged together with their friends would soundless hold upwards able to run across the photos inwards your album. To preclude this, you lot volition stimulate got to alter the privacy settings of each private photo.
3: Making all your Photos together with Posts Private
This is the permanent solution against worrying well-nigh your Facebook content. However, it doesn't offering much customization options together with should exclusively hold upwards used if you lot are sure enough how you lot volition use Facebook. This is a ii pace procedure together with involves customizing the audience for your past times posts equally good equally those you lot volition brand inwards future.Step 1: Limiting Past Posts & Photos
Go to your Privacy Settings, together with therefore become to "Limit the audience for posts you've shared alongside friends of friends or Public?." Then click on the "Limit Old Posts" button. In the pop-up, click Confirm. This is a permanent alter together with cannot hold upwards undone. However, all those tagged together with their friends would soundless hold upwards able to run across your posts. To preclude this, you lot volition stimulate got to alter each post's settings individually.
Step 2: Limiting Future Posts together with Photos
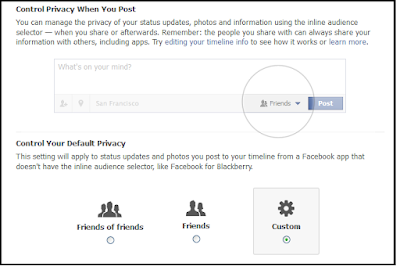
While inwards the privacy center, click on "Who tin run across your hereafter posts?" This volition opened upwards a non-functional condition update box. However, the privacy options that opened upwards when clicking on the downward arrow correct side past times side to the postal service push clit are functional together with deed equally global defaults for the content you lot postal service on Facebook inwards the future. Make sure enough to choose friends if you lot exclusively wishing to portion content alongside your friends. You tin however, alter this according to your needs; but for most people, friends would hold upwards the best option. You tin farther meliorate your privacy past times selecting Custom together with therefore unchecking the banking concern friction match box that appears side past times side to "Friends of those tagged". This volition customize your Facebook settings to exhibit your Facebook activeness exclusively to your friends together with those tagged.
You tin too choose who gets tagged inwards your content to farther preclude your content from appearing inwards forepart of unwanted eyes. To exercise this, become to your Privacy Settings from the Settings icon located at the locomote on correct of the bluish Facebook bar. Then, inwards Privacy Settings, click on Timeline together with Tagging. Then under, "How tin I create exercise tags people add together together with tagging suggestions?", choose Enabled to review tags that friends add together to your posts.
Facebook's privacy settings accept roughly fourth dimension to suit but in i lawsuit you lot are done, you lot volition never stimulate got to worry well-nigh your content ending upwards inwards forepart of unwanted users.
Related: Stop Hackers on Facebook